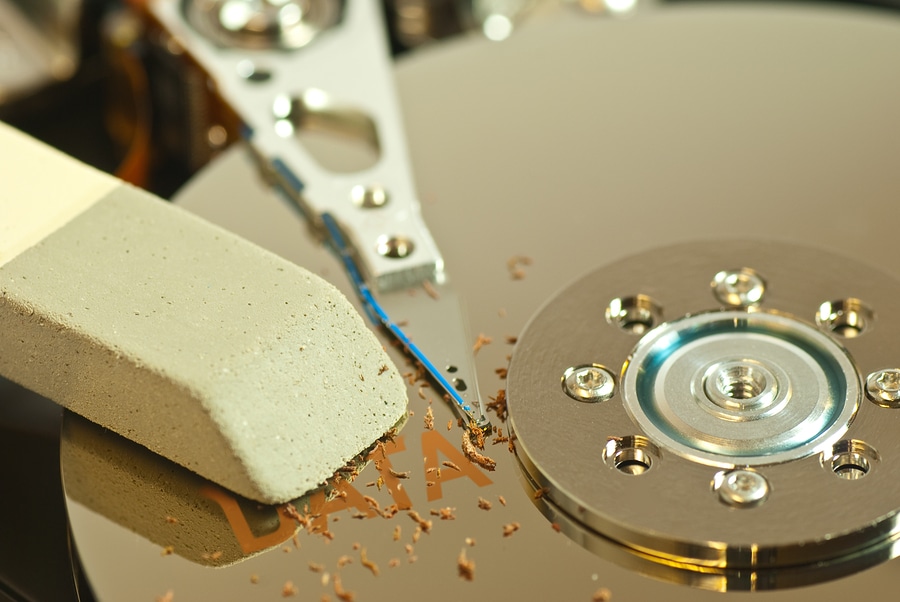
What is DOD-Level Data Wiping?
There are a couple of reasons why you might want to wipe data from hard drives or other devices used to store confidential information. First, you probably pass devices along to new employees rather than getting rid of them, and you don’t want to allow access to existing data or permissions.
Second, your South Dakota business may be interested in refurbishing and remarketing older devices when you upgrade to newer ones. Naturally, you don’t want new owners getting their hands on your sensitive business information, and you are legally responsible for keeping consumer data private.
This means you need to eliminate any and all data on devices, in keeping with applicable consumer privacy laws, at the least. Of course, not all data holds equal importance. For certain types of data, stricter security measures apply.
Whether your industry has higher standards for data destruction or you simply want to go above and beyond to wipe data from devices before you remarket them, you should consider DOD-level data wiping. What makes this form of wiping superior to standard methods?
DOD-Level Compliance
Many government organizations are held to extremely high standards when it comes to data security because of the sensitive nature of information they keep. The Department of Defense (DOD), in particular houses crucial government secrets that could, if leaked, compromise the very security of our nation.
So, what do they do with their IT assets when they have to upgrade to new equipment? They observe stringent wiping methods that ensure total elimination of data.
While DOD methods may seem like overkill to the average business owner, there’s no denying the results. When you undertake a DOD-level wiping process, you’re certainly going to comply not only with federal, state, and local privacy laws, but you’ll likely exceed industry regulations designed to protect medical, financial, and other extremely sensitive data.
Three-Pass Overwrite
The DOD actually uses two different levels of wiping. Even the first, the three-pass overwrite, should go beyond what the average business needs. By this method, wiping occurs in three phases. The first pass overwrites all existing data with a series of zeros, while the second pass uses a series of ones. The third and final pass is made using a random character to overwrite data, before a verification pass is conducted to ensure that no trace of the original data remains.
Seven-Pass Overwrite
If three passes just aren’t enough to quell nagging doubts about wiping data, good news – there’s also a seven-pass process that overwrites data as follows:
– Pass 1: zeros
– Pass 2: ones
– Pass 3: random character
– Pass 4: a different random character
– Pass 5: zeros
– Pass 6: ones
– Pass 7: a random character
This process is followed by a final pass to verify data elimination. For most companies, the time and cost associated with this lengthy process aren’t necessary, but it’s always good to know your options when it comes to protecting your company and your customers.
If you’re seeking professional help wiping data so you can remarket devices, contact the experts at SEAM today at 605-274-7326 (SEAM) or online to learn more and request a quote.
SEAM provides IT recycling and data destruction services including onsite shredding and hard drive wiping to South Dakota, North Dakota, Minnesota, Iowa, and Nebraska.
Schedule a pickup or contact us for more information.





